
Linkedin Learning – Ethical Hacking-Scanning Networks (2023)
English | Tutorial | Size: 261.04 MB
After footprinting and reconnaissance, scanning is the second phase of information gathering that hackers use to size up a network.

Linkedin Learning – Ethical Hacking-Scanning Networks (2023)
English | Tutorial | Size: 261.04 MB

Udemy – Crafting Nmap Scripts Advanced Network Scanning
English | Tutorial | Size: 1.98 GB

Udemy – Real NMAP Elite Network Scanning Reconin 10 Hours CNMP
English | Tutorial | Size: 5.45 GB

Linkedin Learning – CompTIA PenTest PT0-002 Cert Prep 2 Information Gathering and Vulnerability Scanning-XQZT
English | Tutorial | Size: 3.02 GB
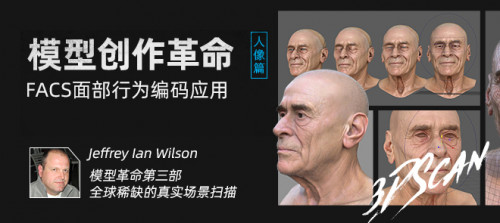
Yiihuu – Film and Game Model 3D Scanning Modeling Technology Learning Manual-FACS Portrait
English | Size: 2.5GB
Category: Tutorial