
LinkedIn Learning – Go Practice – Error Handling
English | Tutorial | Size: 21.65 MB
Effective error handling is one of the most important skills you can have to ensure that your server doesn’t completely crash if something goes wrong.

LinkedIn Learning – Go Practice – Error Handling
English | Tutorial | Size: 21.65 MB

Pragmatic Ai – 52 Weeks of Swift Episode 16-error Handling-iLLiTERATE
English | Tutorial | Size: 446.36 MB
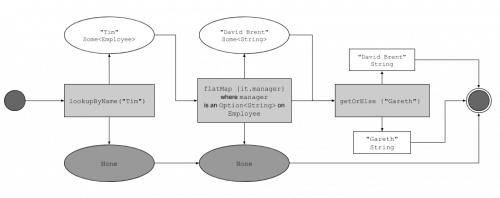
Manning – Functional Error Handling Without Exceptions in Kotlin-iLLiTERATE
English | Size: 3.37 GB
Category: Tutorial
PluralSight – Error Handling In C Sharp 10 Bookware-KNiSO
English | Size: 221.54 MB
Category: Tutorial