PluralSight – Defense Evasion With Proxychains Bookware-KNiSO
English | Size: 45.93 MB
Category: Tutorial
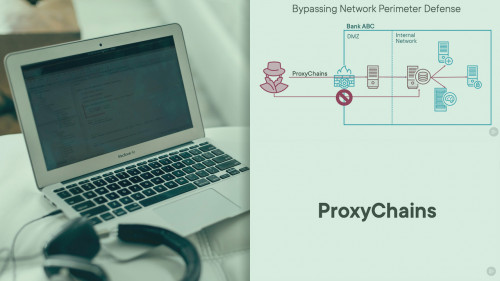
Network security tools are the most common line of defense in a company. In this course, you will learn how to use ProxyChains to re-route your network traffic and bypass such security tools
Virtually every company has a at least a firewall solution to prevent hackers from accessing internal servers. As a red team specialist, you job is to simulate a real attack and try to bypass such defense mechanisms. In this course, Defense Evasion with ProxyChains, you will learn how to bypass network defense tools by tunneling the traffic through compromised machines. First, you will explore what network defense evasion is and how ProxyChains can help you to accomplish that. Then, you will see how to obfuscate your real IP address by using ProxyChains and the TOR network. Finally, you will learn how to bypass network segmentation and firewall solutions by using ProxyChains to re-route your traffic through an already compromised machine. This course covers a tactic from the MITRE ATT&CK framework: Network Boundary Bridging (T1599).
Install Notes: Unrar, Learn and Enjoy!
GREETINGS:
KNOWN – HONOR – SKIDROW – DARKSiDERS – DAUDiO – JAVSiDERS – dbOOk – z0ne

RAPIDGATOR
rapidgator.net/file/8186338b17eadd3b765dcbb7d27caf46/PluralSight.Defense.Evasion.With.Proxychains.Bookware-KNiSO.rar.html
NITROFLARE
nitroflare.com/view/074F3CBA711647E/PluralSight.Defense.Evasion.With.Proxychains.Bookware-KNiSO.rar